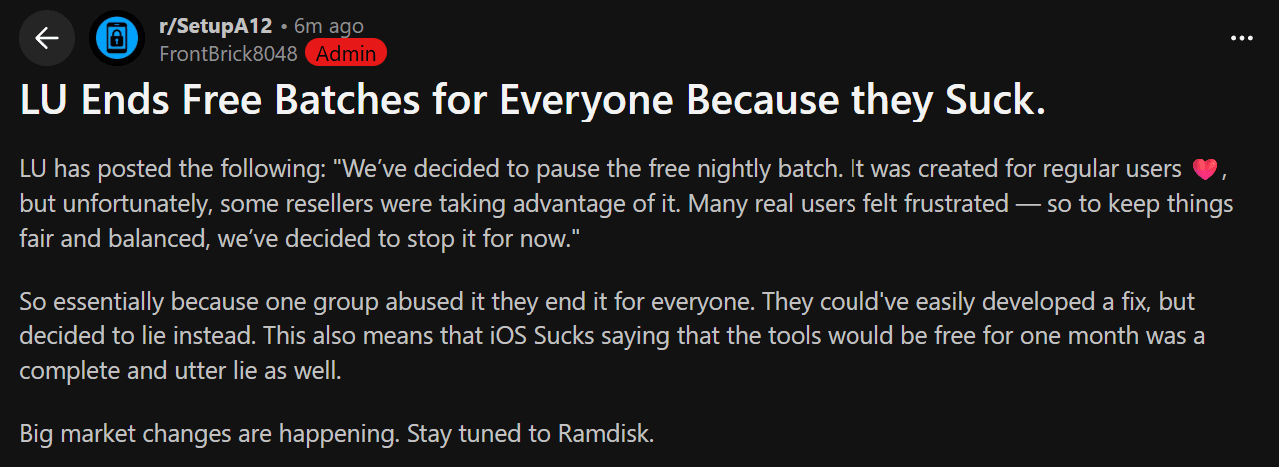
LegitUnlocks Makes Bold Claims; Get's DDoSed (Not Really)
Unpacking what looks like more fake bait.

This afternoon, LegitUnlocks made many bold claims, and then decided to fake a DDoS attack. Let’s unpack these.

The first claim seems bogus. Having bypassed many devices on many tools myself, I have not seen this issue happen once. LU provides little evidence to this, and even if tools did it doesn’t pose any real problems. You can read more about that here.
Suffice it to say, this claim is not grounded in reality.

18 second later, LU posted this.

This DDoS attack is verifiably false. Here’s some reasons how we know this.
The Message Formatting
First, it looks like they are paying attention to this blog; they increased the RPS needed to “trigger” protection against a “DDoS” attack on their servers.

You can see here that the RPS threshold changed from 10 to 60. This is actually our first reason why this may be fixed. The formatting of this last line is off.
Old Line: Traffic max RPS threshold 10 passed by loc b’/’
New Line: Traffic max RPS threshold [60] passed
The message formatting has changed. Is this because of setting changes on their servers or is because of faking the message? We’re not sure. That’s not the only evidence we havem however.
Timestamps are completely off.

Note the timestamp in this original post. 8 seconds into 4:01 this post was made. LU claims this DDoS happened after the post, and likely because of it.

The timestamp here is made two seconds BEFORE the post was made, and twenty seconds before the “free” post was made. Not to mention, this detection wouldn’t have been instant. It likely (if it even happened) happened ~10-20 seconds beforehand.
Conclusion
This isn’t rock-solid evidence, but it’s certainly suspicious. LegitUnlocks has engaged in this sort of sketchy behavior in the past, and It’s not impossible that they’d do it again. Until we have more evidence, stay tuned.